India In A Digital World Where The Cost Of Sensitive Personal Data Is Just Rs 500

- PNB Data Breach – 10,000 Credit and Debit Card Details Compromised, February, 2018
Punjab National Bank suffered a data breach affecting as many as 10,000 debit and credit card accounts, reported Asia Times in February, 2018.
According to the Asia Times report, security experts at that time believed that sensitive information of card holders was made available for purchase through a website for at least three months. It also added that the state-run bank did not detect the data breach until it was informed by CloudSek Information Security.
Information such as names, expiry dates, Personal Identification Numbers and Card Verification Values were released online, the report said. Relevant agencies had been alerted and they were trying to establish the extent of the problem, said Asia Times, quoting government official who were aware of the breach.
- State Bank of India Forgets to Password Protect its Server, January 2019
In January, 2019, India’s largest bank secured an unprotected server that allowed anyone to access financial information on millions of its customers, like bank balances and recent transactions.
The server, hosted in a regional Mumbai-based data center, stored two months of data from SBI Quick, a text message and call-based system used to request basic information about their bank accounts by customers of the government-owned State Bank of India (SBI), the largest bank in the country and a highly ranked company in the Fortune 500.
But the bank had not protected the server with a password, allowing anyone who knew where to look to access the data on millions of customers’ information.
It’s not known for how long the server was open, but long enough for it to be discovered by a security researcher, who told TechCrunch of the leak, but did not want to be named for the story.
SBI Quick allows SBI’s banking customers to text the bank, or make a missed call, to retrieve information back by text message about their finances and accounts. It’s ideal for millions of the banking giant’s customers who don’t use smartphones or have limited data service. By using predefined keywords, like “BAL” for a customer’s current balance, the service recognizes the customer’s registered phone number and will send back the current amount in that customer’s bank account. The system can also be used to send back the last five transactions, block an ATM card and make inquiries about home or car loans. It was the back-end text message system that was exposed, storing millions of text messages each day.
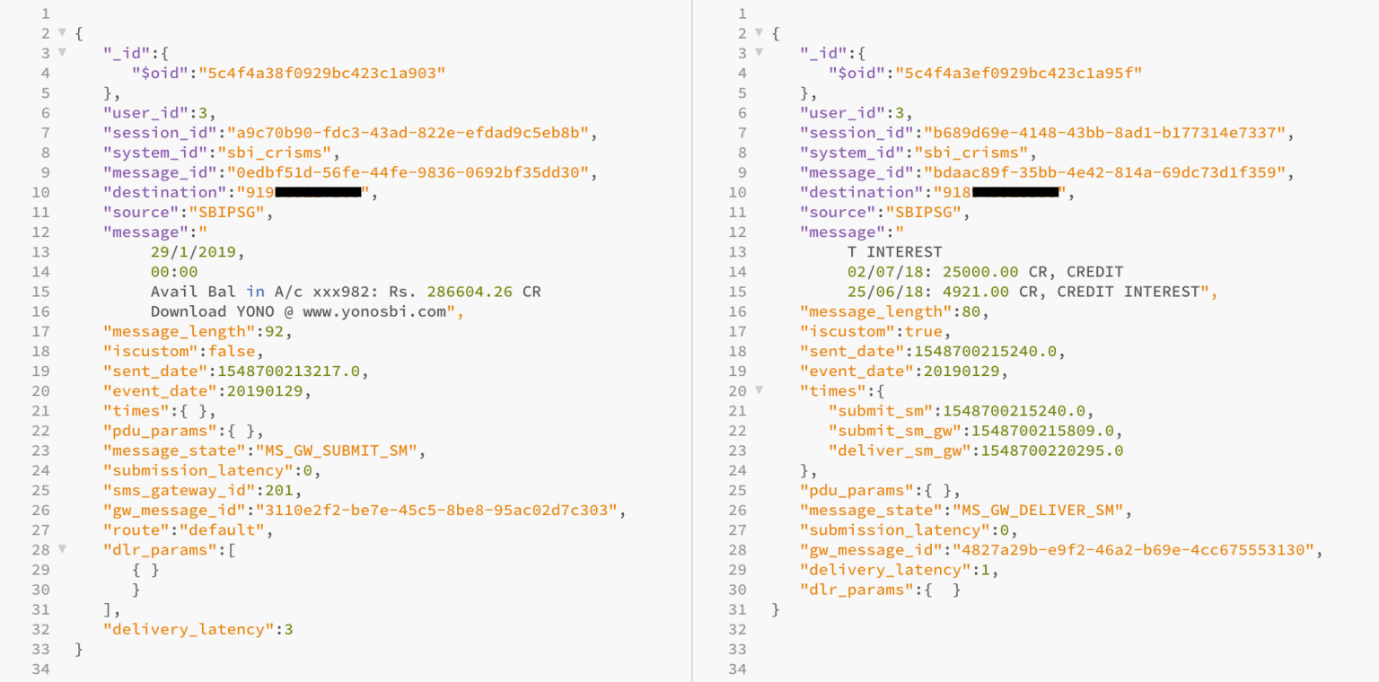
The passwordless database allowed anyone to see all of the text messages going to customers in real time, including their phone numbers, bank balances and recent transactions. The database also contained the customer’s partial bank account number. Some would say when a check had been cashed, and many of the bank’s sent messages included a link to download SBI’s YONO app for internet banking.
The database also had daily archives of millions of text messages each, going back to December, allowing anyone with access a detailed view into millions of customers’ finances.
At that time, TechCrunch had verified the data by asking India-based security researcher Karan Saini to send a text message to the system. Within seconds, they found his phone number in the database, including the text message he received back. “The data available could potentially be used to profile and target individuals that are known to have high account balances,” Saini had said in a message to TechCrunch. Saini had previously found a data leak in India’s Aadhaar, the country’s national identity database, and a two-factor bypass bug in Uber’s ridesharing app.
Saini said that knowing a phone number “could be used to aid social engineering attacks — which is one of the most common attack vectors in the country with regard to financial fraud”.
SBI claims more than 500 million customers across the globe with 740 million accounts.
Just days earlier, SBI had accused Aadhaar’s authority, UIDAI, of mishandling citizen data that allowed fake Aadhaar identity cards to be created, despite numerous security lapses and misuse of the system. UIDAI denied the report, saying there was “no security breach” of its system. (UIDAI often uses the term “fake news” to describe coverage it doesn’t like.)
At that time, TechCrunch had also reached out to SBI and India’s National Critical Information Infrastructure Protection Centre, which receives vulnerability reports for the banking sector. Despite several emails, SBI did not comment prior to publication of the report by TechCrunch.
- Airtel API Security Flaw Leaves Data of 325 Million Subscribers at Risk, December 2019
A security loophole in the one of Airtel’s APIs left the data of 325 million subscribers in India vulnerable. It was Ehraz Ahmed, a cybersecurity researcher, who found that the flawed API allowed anyone to fetch sensitive user information about any of Airtel’s subscribers — and it only took him around 15 minutes.
In addition to disclosing user names and contact information, the leak revealed the IMEI number of the user’s device. IMEI is a unique code used by network operators to identify valid devices — if the phone is flagged as stolen, they can cut off services.
“There was a technical issue in one of our testing APIs, which was addressed as soon as it was brought to our notice,” an Airtel spokesperson had told the Business Insider back then.
“Since these were testing APIs, we can now confirm that no data related to our customers has been impacted. Airtel’s digital platforms are highly secure. Customer privacy is of paramount importance to us and we deploy the best of solutions to ensure the security of our digital platforms,” it added.
- Personal Data of 3.4 Million Dunzo Users Exposed, July 2020
In July 2020, Dunzo confirmed a massive data breach in which the personal information of users such as the mobile number and email address was exposed. In an internal investigation, the delivery service provider discovered that information compromised contained additional Personally Identifiable Information (PII) data as well.
Dunzo explained that affected information included details such as last known location, phone type, last login dates. The company further found that the database also contained advertising-related attributes including a few specific PII — device info, last known IP address, and advertising id. Earlier the company confirmed that phone numbers and email address of users were exposed.
The delivery service provider explained that the servers of a third party it works with were compromised and this allowed the attacker to get unauthorized access and breach into Dunzo’s database. The company also revealed that no users’ home addresses were compromised during this data breach.
- Massive Data Breach in PayTM Mall, Hackers Demand Ransom, August 2020.

E-commerce platform Paytm Mall had suffered a massive data breach, where a cybercrime group under the alias ‘John Wick’ was able to get unrestricted access to the entire database of the company, according to US-based cyber-risk intelligence platform Cyble Inc.
According to Cyble, ‘John Wick’ had broken into multiple Indian companies and collected ransom from various Indian organizations including OTT platform Zee5, fintech startups, Stashfin, Sumo Payroll, Stashfin, i2ifunding, through other aliases such as ‘South Korea’ and ‘HCKINDIA’.